In the intricate dance of modern business operations, trust and responsibility are paramount. Entrusting an employee with the keys to your business—whether physical keys, alarm codes, or digital access credentials—is a significant act of faith. It signifies a level of confidence in their judgment, integrity, and ability to safeguard your assets, intellectual property, and operational continuity. However, faith alone is rarely sufficient in the face of potential misunderstandings, security breaches, or legal disputes. This is where a meticulously crafted document becomes indispensable.
A well-defined agreement serves as a foundational pillar, ensuring that both the employer and the key-holding employee are unequivocally clear about their roles, responsibilities, and the expectations associated with this crucial access. It’s not merely a formality; it’s a strategic business tool designed to mitigate risks, enhance security protocols, and foster a transparent work environment. Business owners, HR professionals, and legal teams seeking to formalize these critical access permissions will find immense value in understanding the structure and content of an effective employee key holder agreement template.
The Imperative of Clear Documentation in Today’s Business Landscape
The complexity of contemporary business operations demands precision in every aspect, particularly concerning security and access control. Gone are the days when a verbal understanding sufficed for key-holding responsibilities. Today’s legal and operational environment necessitates explicit, written documentation to protect all parties involved. A clear agreement provides a legal framework, outlining the specific terms and conditions under which an employee is granted access to company premises, property, or sensitive information.
Without such a document, businesses leave themselves vulnerable to a myriad of risks. Misunderstandings about security protocols, accountability for lost keys, or unauthorized access can quickly escalate into costly incidents, legal liabilities, or reputational damage. This formalized approach establishes a benchmark for conduct, ensuring that employees understand the gravity of their responsibilities and the potential consequences of non-compliance, thereby safeguarding the company’s assets and operational integrity.
Core Benefits of a Standardized Agreement
Implementing a standardized agreement for employees entrusted with key-holding duties offers a wealth of advantages beyond mere legal compliance. Firstly, it fosters consistency across your organization. Every employee granted key-holder status operates under the same set of expectations and rules, simplifying training, management, and enforcement. This consistency minimizes confusion and promotes a uniform standard of security.
Secondly, a robust employee key holder agreement template acts as a powerful tool for risk mitigation. By explicitly defining responsibilities, it reduces the likelihood of security breaches, theft, or damage to company property. Should an incident occur, the agreement provides a clear basis for investigation and disciplinary action, offering a layer of legal protection to the employer. Moreover, it empowers employees by clearly delineating their roles, providing them with the confidence that they understand their obligations and the company’s expectations, ultimately contributing to a more secure and accountable workplace.
Tailoring the Agreement for Diverse Operational Needs
While a standard template provides an excellent starting point, its true strength lies in its adaptability. Businesses operate across a vast spectrum of industries, each with unique security concerns, access requirements, and operational procedures. A generic document might overlook industry-specific nuances, potentially leaving critical gaps in your security framework. Therefore, customizing the agreement for your particular context is not just recommended, but essential.
For instance, a retail business might focus on opening and closing procedures, cash handling, and alarm system protocols. A healthcare facility, conversely, would emphasize securing patient records, controlled substances, and sensitive equipment, alongside general facility access. A tech company might prioritize data center access and intellectual property protection. The template should be flexible enough to incorporate specific details like designated access hours, specific areas the employee can enter, procedures for activating/deactivating security systems, and protocols for reporting suspicious activity or security incidents. This bespoke approach ensures the document accurately reflects the unique risks and responsibilities pertinent to your enterprise, making it a truly effective and relevant security measure.
Essential Components of a Robust Key Holder Agreement
To be truly effective and legally sound, any key holder agreement must contain several critical clauses that clearly outline expectations, responsibilities, and consequences. These components form the backbone of the document, ensuring comprehensive coverage and mutual understanding.
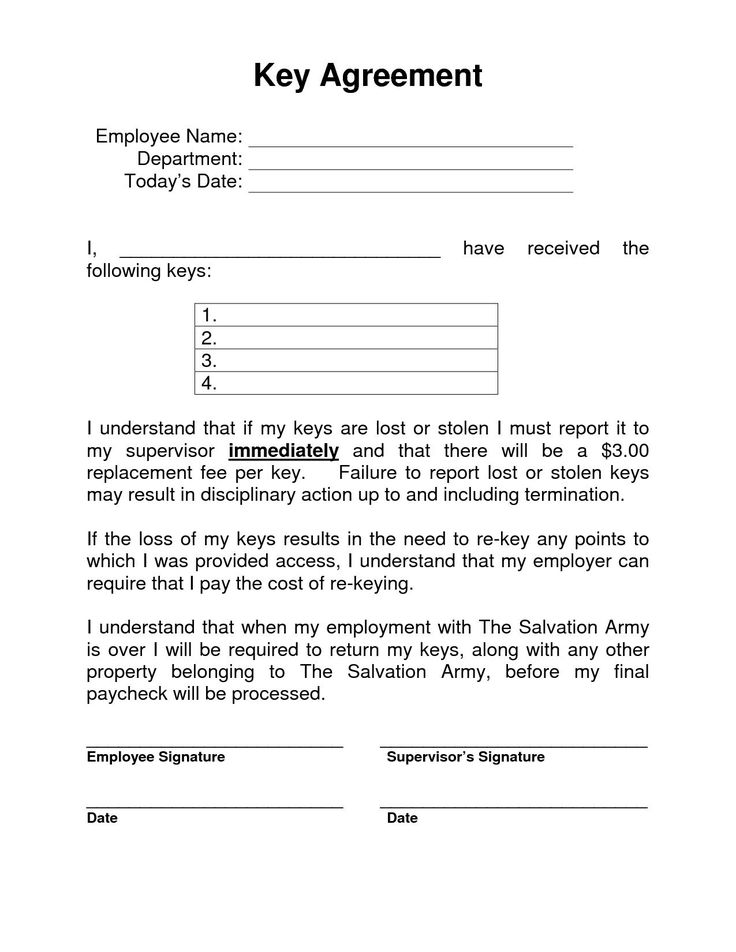
- Identification of Parties: Clearly state the full legal names of the employer and the employee entering into the agreement.
- Purpose of Agreement: Briefly state the objective of the document – to formalize the terms and conditions for the employee’s access to company property.
- Scope of Access and Responsibilities: Detail the specific keys, access cards, alarm codes, or digital credentials issued. Explicitly define the areas the employee is authorized to access, the times of access, and their precise responsibilities (e.g., locking doors, setting alarms, turning off lights).
- Security Procedures and Protocols: Outline strict guidelines for handling keys/codes, including prohibitions against lending them to others, making duplicates, or sharing access information. Specify procedures for reporting lost, stolen, or compromised keys/codes immediately.
- Confidentiality and Data Security: If access implies exposure to sensitive company information, client data, or intellectual property, include a confidentiality clause emphasizing the obligation to protect such information.
- Acknowledgment of Responsibility: A clause where the employee explicitly acknowledges their understanding of the terms and their commitment to uphold all security measures and procedures.
- Return of Company Property: Mandate the immediate return of all keys, access cards, and any other company property upon termination of employment or cessation of key-holding duties.
- Consequences of Non-Compliance: Clearly state the disciplinary actions, up to and including termination of employment and potential legal action, for failure to adhere to the agreement’s terms, security breaches, or unauthorized access.
- Indemnification: A clause protecting the company from liability for unauthorized actions by the key holder or for damages resulting from their negligence.
- Governing Law: Specify the state laws that will govern the agreement, which is crucial for legal enforceability in the US.
- Signatures: Spaces for the employee’s signature, the employer’s authorized representative’s signature, and the date, confirming mutual acceptance of the terms.
Optimizing for Clarity and User Experience
Beyond the legal substance, the presentation and readability of your key holder agreement are paramount. A document that is difficult to navigate or understand diminishes its effectiveness, regardless of how robust its clauses may be. Prioritize clear, concise language, avoiding overly technical jargon where possible. The goal is for every employee, regardless of their legal background, to fully comprehend their obligations.
Use headings and subheadings to break up long blocks of text, creating a logical flow that is easy to follow. Bullet points, as demonstrated above for the essential clauses, are excellent for listing responsibilities or procedures, enhancing readability. Ample white space around text and between paragraphs prevents the document from appearing daunting. For digital use, ensure the document is easily searchable and accessible across various devices. If printing, use a legible font size and consider a format that can be easily bound or filed. Implementing version control (e.g., “v1.1, Effective Jan 2024”) is also crucial to ensure everyone is working from the most current iteration of the agreement, especially after updates or revisions.
In an era where security threats are ever-evolving, a clearly communicated and easily digestible agreement is an indispensable asset for both the employer and the key-holding employee. It serves as a cornerstone of your internal security policy, fostering a culture of accountability and protection.
The proactive adoption of a well-structured employee key holder agreement template is a testament to an organization’s commitment to security, transparency, and operational excellence. It transforms a potentially ambiguous responsibility into a clearly defined, mutually understood obligation, safeguarding both the company’s physical assets and its legal standing. By investing the time to implement and customize such a document, businesses effectively fortify their defenses against common security vulnerabilities and potential liabilities.
Ultimately, leveraging an employee key holder agreement template is more than just a procedural task; it’s a strategic investment in peace of mind. It provides a reliable, professional framework that not only protects valuable assets but also cultivates a trusting and responsible work environment, ensuring that critical access is managed with the diligence and clarity it demands.